Disclaimer: This is not financial advice. Anything stated in this article is for informational purposes only and should not be relied upon as a basis for investment decisions. Triton may maintain positions in any of the assets or projects discussed on this website.
TL;DR
The Risks are Real
Likely to no reader’s surprise, crypto isn’t all sunshine and rainbows.
As with the internet, open global systems inevitably come with people looking to prey on others. And in what may be the understatement of the decade: crypto is definitely no exception. This segment will take a look at some of the major issues that are still plaguing the industry, providing fair reason to be very cautious when investing in and using the technology. Importantly, this will highlight why best practices for custody, risk management and diligence are of paramount importance when investing in digital assets, especially as the infrastructure continues to be built out.
First and foremost: the blockchains themselves have thus far proven to be highly robust – Bitcoin, Ethereum, Solana, Base, and most other serious networks – have never been hacked. That is, the ability to hold BTC, ETH or SOL and send those native assets on the networks is highly secure. Bitcoin is a $2 trillion honey pot for hackers and yet has never been exploited. Could this change in the future? Sure, any software can theoretically be hacked given enough compute power but the difficulty of doing so renders it effectively impossible today, as we’ll explain in this post.
Let’s first take a look at the major risk vectors for blockchains themselves to understand why they have been secure to date, and where potential issues may arise in the future.
To start: what does ‘hacking’ a blockchain even mean? If we think back to what blockchains are in the first place – they are cryptographically secured append-only ledgers consisting of blocks of transactions that are collectively updated and agreed upon by a distributed set of nodes on the network. As such, there are three primary ways a chain can be exploited: comprising the consensus mechanism, comprising the networking layer, and comprising the actual cryptographic protocols securing the chain.
The primary form of consensus exploit is what is referred to as a ‘51% attack’. That is, a malicious actor is able to secure more than 50% of a network’s ‘processing’ power, and by doing so, gain the ability to reorder transactions, double-spend coins or censor new transactions from being included. To date, this has yet to happen for any major canonical chain with real activity as it is incredibly difficult and costly to do so. A chain’s inherent ability to operate even in the face of some subset of malicious nodes is generally known as ‘Byzantine Fault Tolerance’. Recall our discussion about how blockchains have created novel consensus mechanisms to overcome what in game theory is known as the Byzantine General’s problem.
Bitcoin uses a proof of work (PoW) consensus mechanism, where miners around the world all compete to solve increasingly difficult math problems. This problem essentially requires brute force guess and checking to solve and is incredibly computationally intensive to do so, but once a solution is found, is trivially easy for the other nodes to verify. The winning miner broadcasts the solution and the block of unconfirmed transactions to the network, which is then validated by the other nodes. Once confirmed by a majority, that block is added to the chain and the process repeats, taking roughly 10 minutes to produce each block. The difficulty of the puzzle is automatically adjusted by the network roughly every 2 weeks to maintain a consistent block time. Given that the difficulty generally increases, the amount of computing power required to solve the puzzle increases as well. When the network first launched, a miner was able to solve the problem on a personal laptop CPU. Today, it requires industrial-level data centers with custom ASICs to regularly win a block. This is why Bitcoin requires such an immense amount of power to operate but is also why Bitcoin is so secure. A 51% attack means that a malicious actor would need to control 51% of the network’s total hashrate in order to exploit the chain – an increasingly difficult proposition as the computing power on the network grows. When one hears talk of Bitcoin’s security budget, they are speaking about the network issuance that incentivizes the continued hashrate required to secure the network.
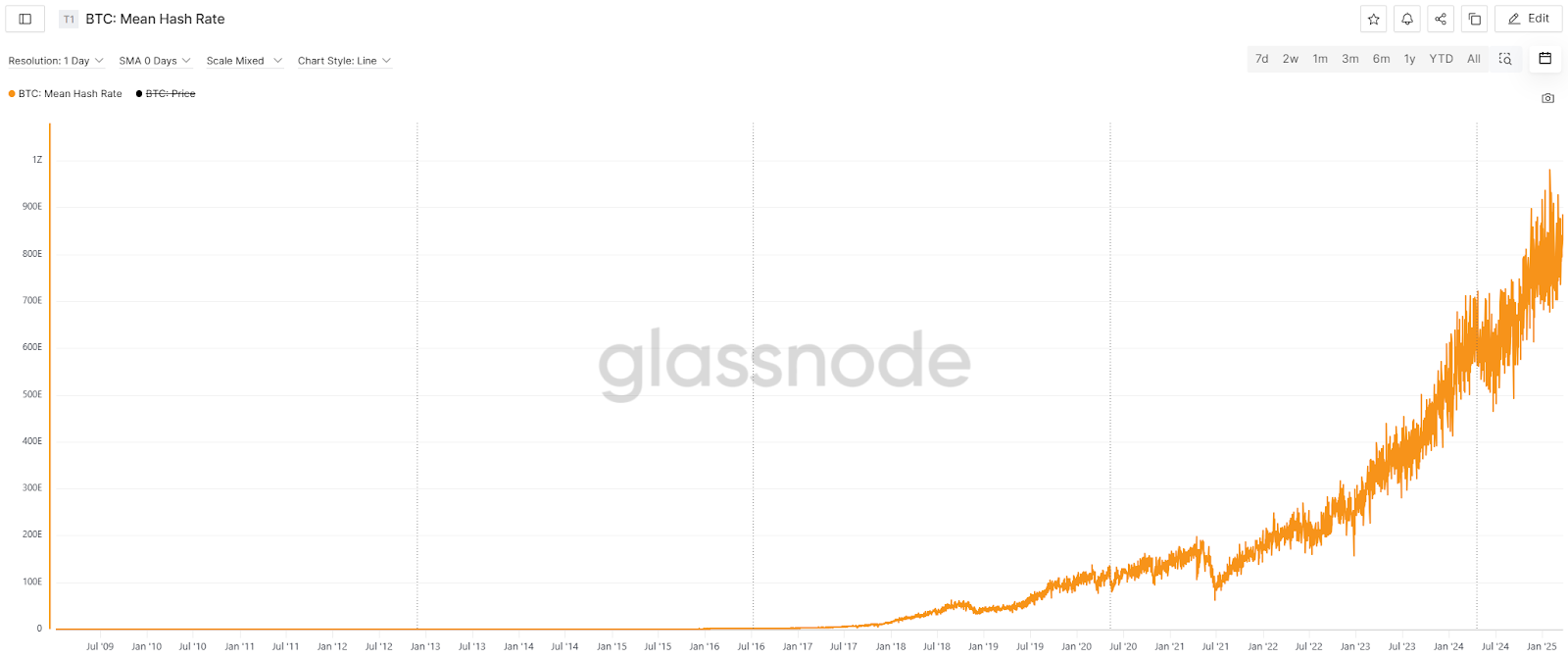
Mean network hashrate on Bitcoin is increasing at an exponential rate per Glassnode
Bitcoin is relatively unique in its use of proof of work for its consensus mechanism today. Ethereum initially used proof of work but switched to its current proof of stake (PoS) consensus mechanism in 2022. Variations of proof of stake are what the vast majority of blockchains use now, but we will focus on Ethereum here as a general example. With PoS, nodes on the network (called validators) are required to post a defined amount of ETH in order to participate in network validation, through a process called staking. That amount is currently set at 32 ETH (roughly $65,000 at current prices). That ETH stake is deposited in order to guarantee that the validator will act honestly. As a function of the staked ETH, validators are randomly chosen to propose new blocks of transactions for inclusion. After the chosen validator proposes a block, other validators on the network review and attest to that block being valid at which point it is added to the chain. 2/3 of validators are required to attest to the validity to make the block final. If a validator tries to propose an invalid block or is offline and unable to participate, a portion or all of the 32 ETH that the validator posted is slashed by the network as a penalty, thus levying a real financial penalty for misbehavior. So, in order to exploit the consensus mechanism of Ethereum, an attacker would need to acquire an immense amount of stake on the network in order to alter blocks or censor transactions. Currently, there are roughly 1,000,000 validators with ~$70B in ETH staked securing the network. This represents Ethereum’s security budget and is why it is seen as being so secure. As an added bonus, this is a far, far less energy intensive mechanism to use, and when Ethereum switched to PoS, it cut the network’s energy footprint by 99.9%. (As a side note: when critics point to the energy use of ‘crypto’, they really mean of Bitcoin specifically. Ethereum and almost every other network requires orders of magnitude less energy).

More than 1,000,000 validators are collectively securing the Ethereum network
Because these are peer-to-peer networks, malicious actors may attempt to exploit the networking layer that facilitates node communication. Most often, this would be in the form of attempting to isolate a node or subset of nodes from the rest of the network and try to feed them incorrect or malicious data that could then be included. Most networks have multiple layers of redundancies and protocol-level checks in place to prevent this, but if successful, this would likely lead to delayed block propagation or the inclusion of a double-spending transaction (i.e. being able to spend the same asset in two separate transactions). Given that blockchains require a majority of nodes to agree to the longest canonical chain, an exploit like this would likely have minimal impact on the overall network in the long run.
Finally, attackers may try to exploit the cryptography of the blockchain itself at the protocol level. Specifically, this means comprising the SHA-256 and ECDSA cryptographic primitives. Both of these are widely used in cryptography far beyond blockchains, and based on current computational abilities, are theoretically impossible to break (hence their widespread use in many industries). Any exploit here would have severe consequences for our broader information (e.g. the entire internet) and financial systems and would not be confined to just impacting blockchains. There is some concern that quantum computing may pose acute risk for blockchains given QC’s theoretical ability to crack current encryption. But again, blockchains are not uniquely exposed to this, and instead are at risk in the same way the internet and all of our encryption today is. However, because they are software, blockchains also have the ability to update the cryptography used to secure the network. As such, whenever quantum computing becomes a significant enough threat, these systems can adopt quantum-secure encryption to maintain security. Any change like this naturally introduces new risks to the network but also renders this ‘quantum threat’ somewhat moot in the grand scheme of things.
If, against all odds, an attacker is successful, stakeholders on these networks can collectively agree to roll back certain transactions or ‘fork’ the chain to a new canonical chain that invalidates any malicious behavior. Done through decentralized governance, this is exceedingly rare and exists as an option of last resort to secure these chains. This is the nuclear option, and would be incredibly contentious and difficult to actually effectuate – but not impossible.
There is also an interesting game theoretic view that provides security for these networks. Specifically, the moment an attacker exploits the network, the very value proposition of that blockchain is severely damaged and thus the value of what they attempted to steal is severely damaged as well, and in the case of the network reacting with a re-org, almost worthless. After all, what is the point of owning an entire network if you are the only one that uses it and no one else sees value in it?
All that is to say, these blockchain networks have been specifically designed to be highly secure and robust against a wide range of possible attacks through a combination of mathematics and game theory, and to date, have proven to be up to the challenge. Can that change? Yes, of course. But as of today, with trillions of dollars at stake, they have proven to be safe to use.
Wait, I thought we were talking about all the hacks that have happened?
Many readers will likely pause here, trying to figure out how these claims can be true when there is what feels like a constant barrage of news about crypto hacks and exploits. It is the topic of this segment, after all.
Don’t get us wrong, there have been plenty, there is no denying that: $3.8B stolen in 2022, $1.7B in 2023, and $2.2B in 2024. In fact, here is a list of the biggest all-time hacks or exploits, and they are massive:

Largest crypto-related hacks in history. Notice how many are bridges or centralized companies
But it is important to understand where those hacks occur. We spent the first part of this segment focusing on how secure each blockchain is on its own. Readers may recall in prior posts that we highlighted how the ‘internetworking’ layer and applications are still very much under development. That is, the technology that allows users to access these networks in the first place and to transfer assets from one network to another. Specifically, this means that the vast majority of hacks and exploits happen at the crosschain junction – the internetworking layer that we are still developing, or of companies trying to provide exchange services.
Notice in the table above – each of these hacks were of a a) centralized exchange or company, b) a bridge, or c) an application. It is not the underlying blockchain networks being exploited, but rather, the interfacing layer of those networks. As a quick comparison, these hacks are akin to train or bank robberies in the 1800s. The robbers ‘hacked’ the transportation and storage of the gold; they did not hack the gold itself. As bank vaults and gold transportation became more secure, the number of large gold heists dropped (though still happen even today).
This is why crypto proponents often use the phrase “not your keys, not your coins”. That is, the moment one allows another entity to hold their BTC, ETH, SOL or other asset on their behalf, they are relinquishing control and custody and trusting that entity to securely protect their assets. This also means that an entity that aggregates assets on behalf of many people becomes a target for attackers. Centralized exchanges are the victims of most hacks specifically because of this; they hold and custody funds for millions of customers in ‘hot’ wallets because of the need to have on-demand liquidity for those customers to trade and withdraw. To date, centralized exchanges have also been the primary way for users to move assets from one chain to another. It is exceedingly difficult for true long-term cold storage to be exploited and is how investors should store their assets if they must keep them on a 3rd party platform. Cold storage is to crypto like what a bank vault is to gold; hot wallets are to crypto like what downtown pawn shops are to gold. There is a significant difference in the security and safety between the two.
Protocols that allow for permissionless transfer of assets between chains, called bridges, have also been developed as a way to remove centralized exchanges from the picture. But these too have had significant problems, especially the early implementations of them. As we highlighted earlier in this post and others, networks often use their own implementations of consensus mechanisms and architectures and thus have differing block speeds, time to finality, and requirements to settle transactions. Bridges thus have to find a way to satisfy the requirements of both chains to facilitate a single cross-chain transaction. And when a third chain is added with different mechanisms, that problem now requires ensuring seamless and secure transactions in 6 directions, instead of just 2. This problem naturally compounds. There have been a multitude of ways teams have tried to solve this problem, but it is incredibly difficult and has opened up significant risk vectors that have been exploited for billions. Bridge technologies have come a long way, and exploits are less common now than in the past, but these still present as some of the most vulnerable protocols today. Going back to our (increasingly strained) analogy, bridges act as the way gold is moved between vaults at different banks. Some are more akin to armored trucks with armed guards, while some are closer to teenage couriers on bikes. Again, there are significant differences in the security and safety of bridging technologies.
As we explored in our last segment, Bitcoin is incredibly simple and thus is used primarily for moving the native BTC asset on the network. As such, it is also highly secure for most users. We also explained that most other chains, such as Ethereum and Solana, allow for far more programmability and expressiveness. While this allows for a far broader range of applications and use cases to be built, it also introduces much more risk to the systems given the added complexity.
For example, Ethereum has its own programming language called Solidity that was designed and developed specifically for writing smart contracts on the Ethereum Virtual Machine. While it draws inspiration from existing programming languages that have had decades of development, Solidity itself is almost entirely novel and tailor-made for blockchains. Because of this, it is far less battle-tested than other languages like Python, C# or Rust. Combine this with the fact it is used to build brand-new-to-the-world applications and is known by only a small subset of developers, there naturally arises security vulnerabilities that can and will be taken advantage of.
Further, because these systems are permissionless, there is no limitation on who can build, launch or access an application. As such, there is a wide range of abilities, attention to security, and general capital available to have contract audits performed, resulting in a similarly wide range of safety for applications. This open, permissionless nature also means that it is largely up to the user to do the diligence of the applications and vet the safety on their own. As another comparison, this is akin to asking the average consumer to evaluate the technical security of their bank or stock exchange. This is frankly an absurd ask of the average user and highlights the significant need for better abstraction and development at the app level to protect consumers from potential security vulnerabilities. As investors, we spend an inordinate amount of time vetting teams, reviewing audits and doing our best to ensure the safety of protocols we invest in. But because these teams are operating on the frontier of this technology, mistakes will inevitably continue to be made and exploited. There is zero doubt that investing in crypto is a high-risk activity.
For example, Euler is a highly flexible lending protocol on Ethereum and other EVM chains. Today, it is one of the largest with over $1 billion in total deposits. It also holds the unfortunate distinction of suffering the largest hack of any application and the 11th largest of any blockchain project or company, period. Despite the team being generally considered one of the best in the industry, consisting of experienced blockchain programmers and PhDs, the protocol was exploited for nearly $200 million in 2023. Though they managed to recover all of the stolen funds, this highlights how much risk exists even for the highest quality protocols in the space. They now have an active $7.5 million bounty program to reward anybody who finds a bug in their code, and have had more than 40 security audits performed by the top auditing firms in the world. This is one of the most extensive security programs in the industry, but does it mean they are now immune from another hack? Only time will tell.
But as the industry continues to progress, programming languages, standardized libraries and developer tooling will all continue to improve, and the marginal risk associated with each application will continue to decrease. Better regulation and legal clarity will also provide the much needed scaffolding required to attract even more of the top engineering talent to the space. But that is not to say it is impossible today to build safely: applications such as Aave, with over $30B in deposits, and stablecoins such as USDC and USDT ($200B+ circulating) have never been exploited, and entire networks like Solana and Sui, that use more robust programming languages (i.e. Rust and Move, respectively) provide far safer environments by default.
So, who’s doing the hacking?
The Lazarus Group (funded and run by North Korea) is the biggest culprit, and outside of crypto, are known to be behind numerous hacks over the years, across just about every industry. They are very active in crypto and responsible for some of the largest hacks in the industry’s history, including the latest $1.5B Bybit exchange hack, and a not-uncommon story in crypto is teams having to screen for North Koreans when hiring engineers. Google recently released a report warning of these activities, specifically highlighting increased risks for European and UK based organizations.
Beyond North Korea, there are naturally individuals acting on their own accord, as there is with any cybercrime. How do we know this? Because of the unique ability to track blockchain transactions due to their open and public ledgers. We will focus more on this aspect in a future post, but readers are welcome to trace the movement of the $1.5 billion in stolen funds from the Bybit hack below:

If the public can easily track the movement of stolen funds in a hack, imagine what the FBI can do

Revisiting crypto’s core security, systemic risks, and the evolving landscape of threats and resilience.

Revisiting blockchain fundamentals: layers, tokenization, native assets.

Revisiting blockchain's development, scaling challenges, regulatory hurdles, and emerging opportunities.